During my work, I was auditing a Cordova App and then I saw a plain text password right in the logs. I talked to the developer and it proved that Cordova doesn’t support Keychain by itself. One of the most popular Keychain plugins (also used by this developer) is https://github.com/ionic-team/cordova-plugin-ios-keychain.
Turned out there was a forgotten NSLog call that logged all keychain entries:
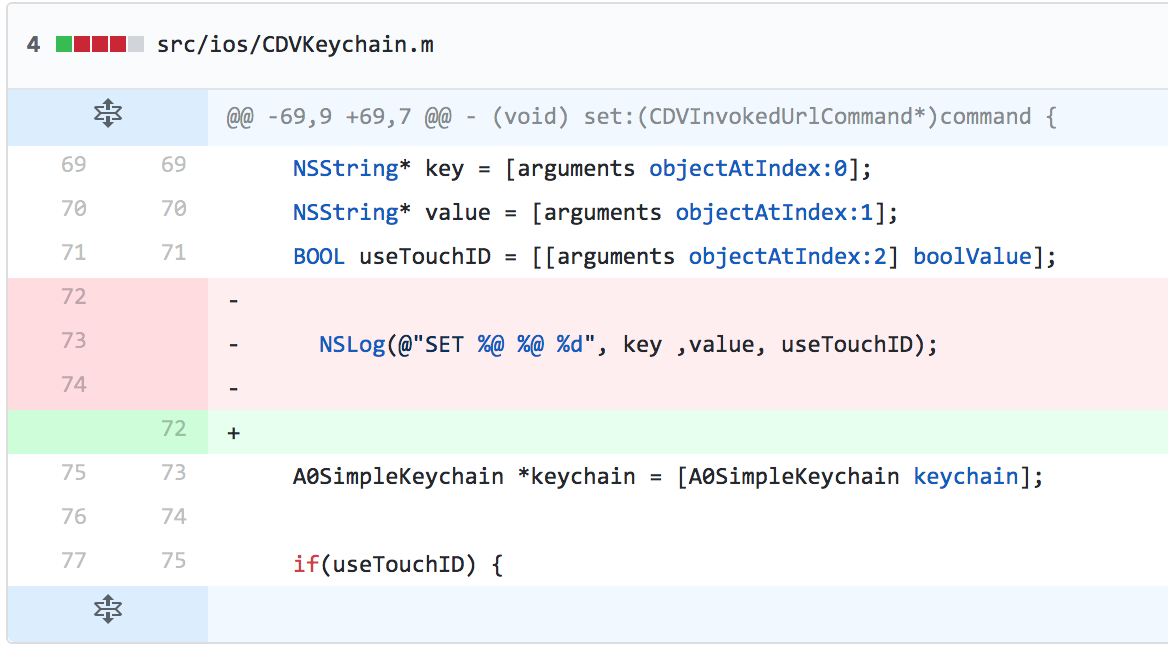
I have reported it and the bug is now fixed (CVE-2018-1000123).