TLDR
Sandbox implemented in macOS does not cover pasteboard. That blog post shows that you can create fully sandboxed malware (that may pass Apple’s review, bypassed many times in the past) stealing & modifying pasteboard values.
What sandbox is?
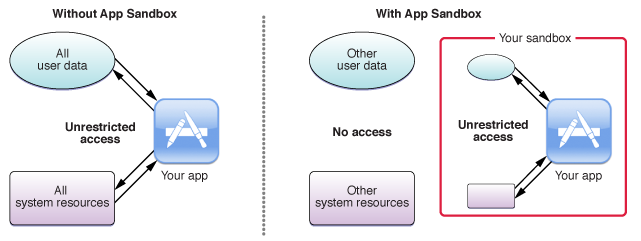
App Sandbox is an access control technology provided in macOS, enforced at the kernel level. It is designed to contain damage to the system and the user’s data if an app becomes compromised. Apps distributed through the Mac App Store must adopt App Sandbox. Apps signed and distributed outside of the Mac App Store with Developer ID can (and in most cases should) use App Sandbox as well. ~ Apple’s documentation
Later we can read that App Sandbox limits access to sensitive resources. But what Apple means by ‘sensitive resources’? There is also an answer to that:
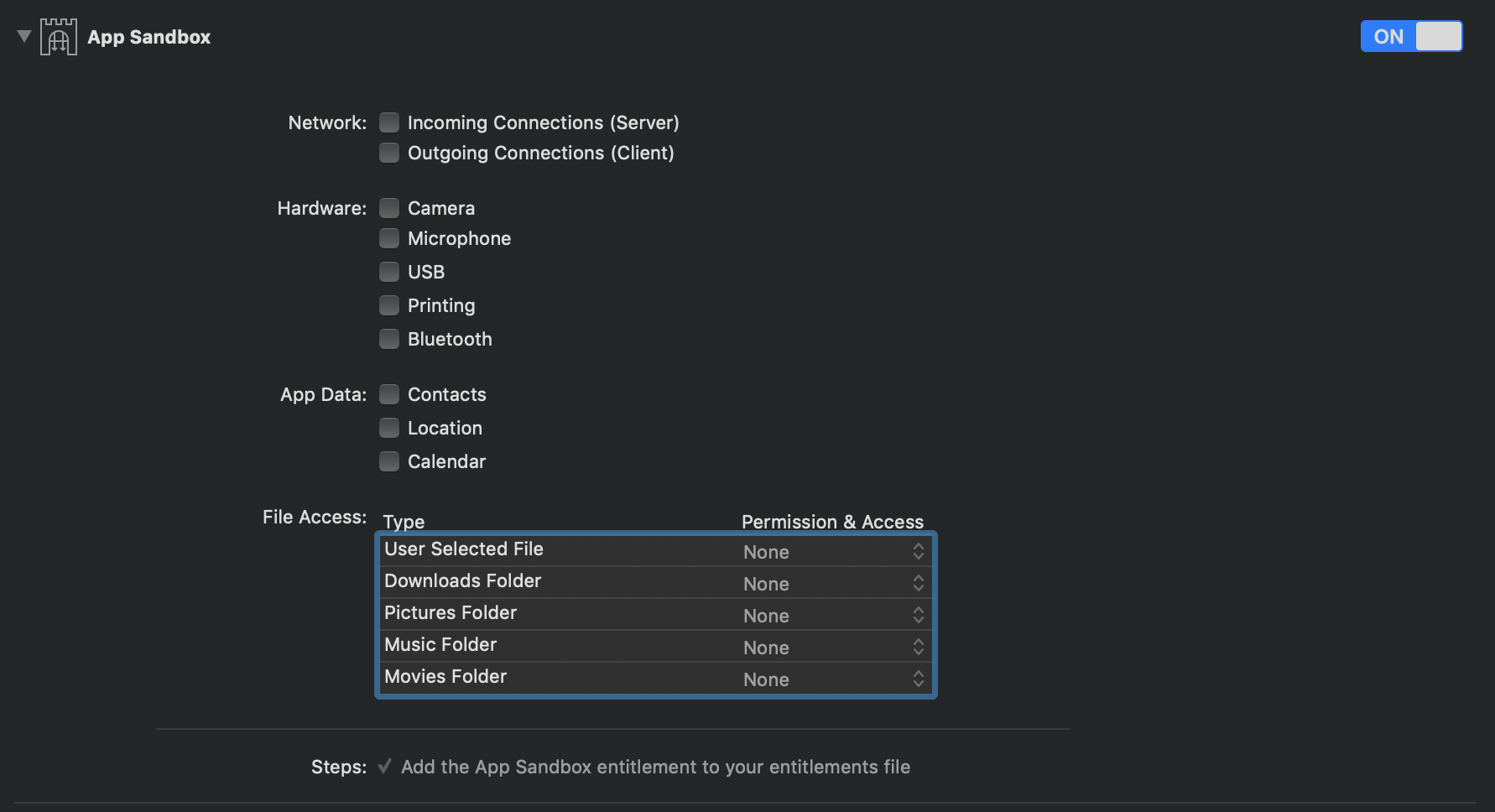
- Hardware (Camera, Microphone, USB, Printer)
- Network Connections (Inbound or Outbound)
- App Data (Calendar, Location, Contacts)
- User Files (Downloads, Pictures, Music, Movies, User Selected Files)
Okay, so pasteboard is not included here.
What can go wrong?
Let’s discuss if pasteboard may be such a resource. What could go wrong if a malicious app had access to our pasteboard? Some examples below:
- Copying&pasting passwords/tokens? - the malicious app may steal that
- Making bank transfer and copying account number? What if malware could modify just copied number and steal your money? (I’m aware that usually, bank will ask you to confirm the provided number, but how many users will just click ’next’?)
- … sending Bitcoins? It’s already happening
- Copying sensitive documents? - 😅
- Or your private photos/videos?
Okay, I believe you may be convinced that pasteboard should be considered as a ‘sensitive resource’.
Coding POC malware!
Let’s find a class responsible for interacting with the system’s pasteboard.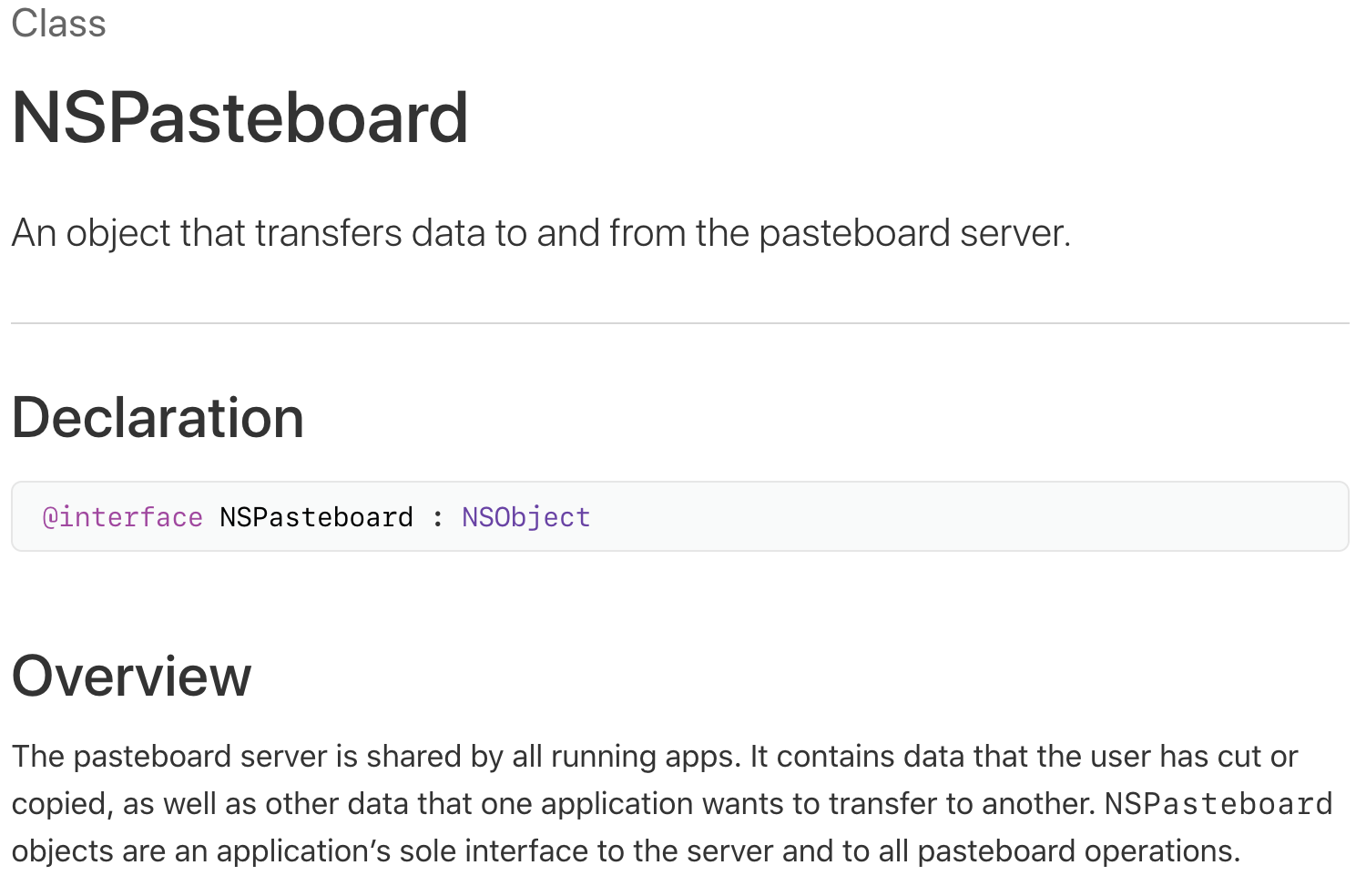
Okay, so we have found one. Now we are going to write some code:
void setPasteboardItem(NSString *str) {
NSPasteboard *pasteboard = [NSPasteboard generalPasteboard];
[pasteboard clearContents];
[pasteboard setString:str forType:NSPasteboardTypeString];
}
NSString* getPasteboardItem() {
NSArray *pb_items = [[NSPasteboard generalPasteboard] pasteboardItems];
NSString *pbi_s;
for(NSPasteboardItem *pbi in pb_items) {
pbi_s = [pbi stringForType:NSPasteboardTypeString];
}
return pbi_s;
}
As you can see, this code sets and gets pasteboard items when their types are string.
Sandboxing the app
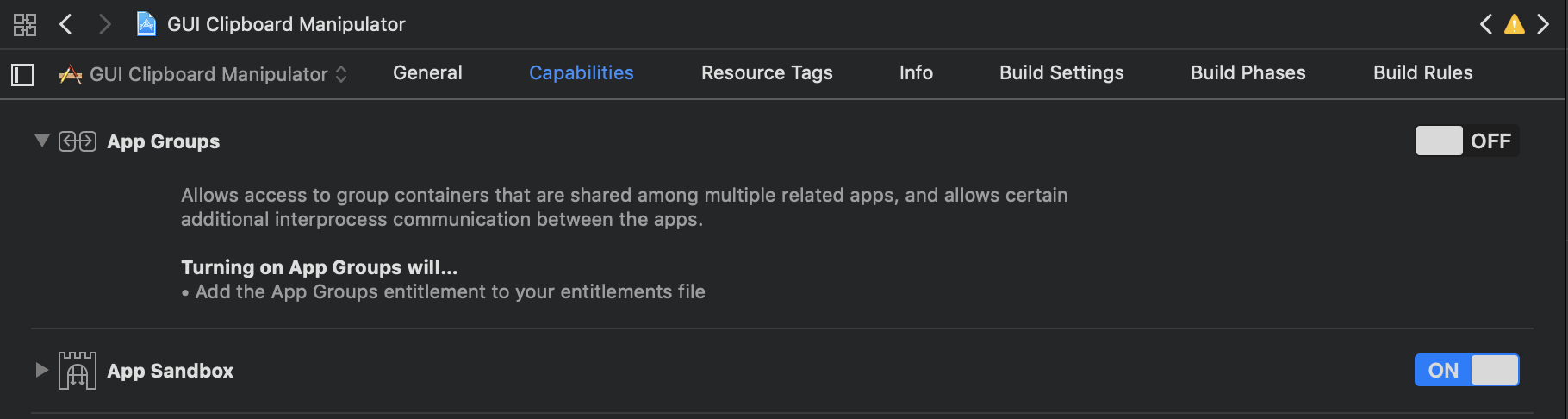
#Beautifying
Let’s add fancy GUI to make this blog post shareable on social media (lol 😂).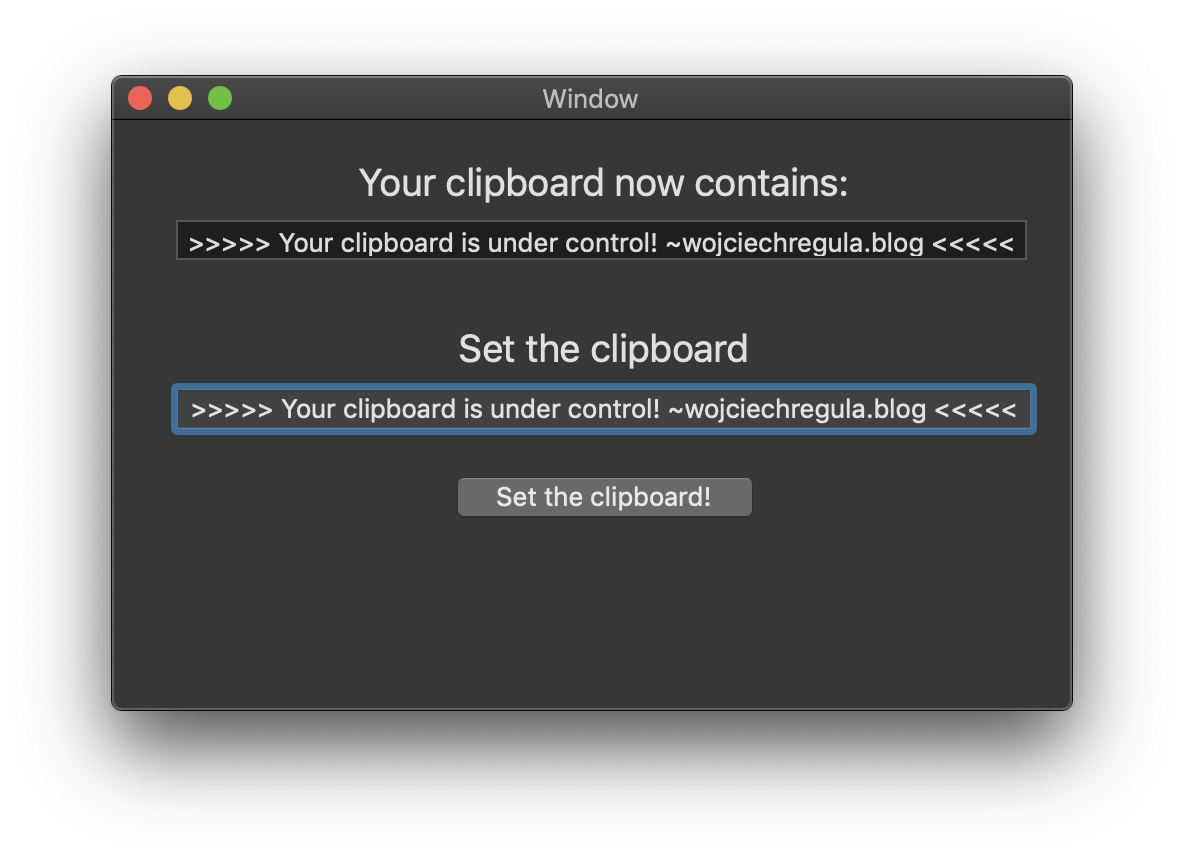
The complete proof of concept

How Apple may fix this?
- The obvious fix is just to extend the sandbox and add a new option to the Xcode sandbox configurator by adding Pasteboard checkbox.
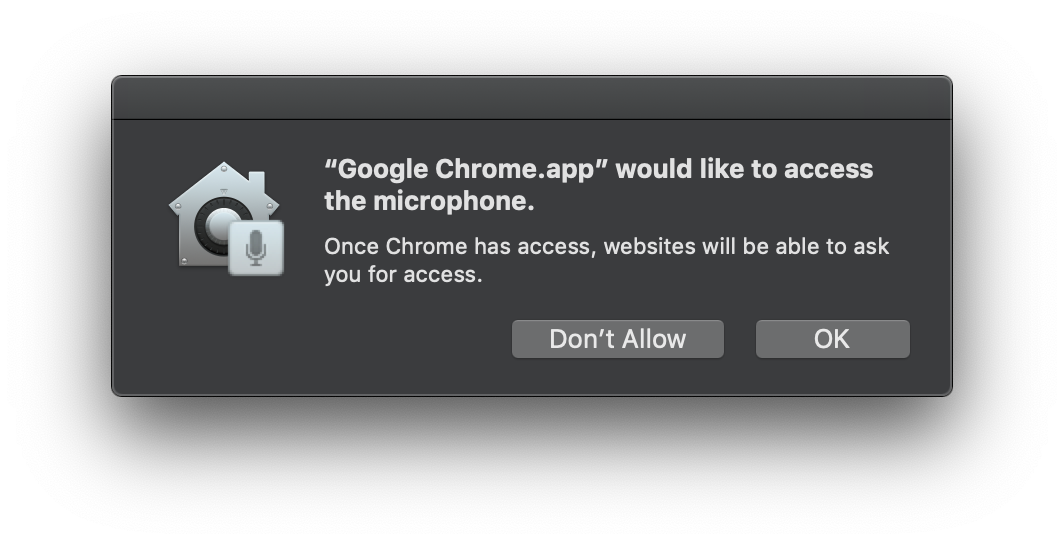
- Use new macOS Mojave feature and ask the user when the app wants to get access to the pasteboard. Current microphone access request example below:
Status
15th December 2018 - Issue sent to Apple
3rd July 2019 - Apple says it is expected behavior.
Shares
Sandboxed malware on #macOS may control your pasteboard https://t.co/LFWY2jEEED via @_r3ggi
— The Hacker News (@TheHackersNews) December 21, 2018